In today’s tech-savvy world of internet, security of personal communications is the important thing than ever before. People are becoming increasingly aware of encrypted messaging, and how outsiders, like hackers, ISP’s or even the government is spying on the content of their messages and theassociated attachments.Conventional texting via SMSis unencrypted, leaving the cracks open for folks to monitor our private conversations for any profiting or law enforcement reason.
In this article, we will be discussing about encrypted messaging application and whyit is necessary in this era, where our personal data is being constantly watched by hackers, Internet Service Providers, and Governmentofficials.
Encryption is basically encoding communications in order to prevent it from prying eyes except its intended recipient. The concept of encryption is quite old, as ancient emperors use to send messages to other generals, by means of simple encryption. Though the encryption used today is way more complicated and safe, the concept is still the same. Modern encryption involves an algorithm referred as cipher for converting data into random symbols or characters. The encrypted data is unreadable for anyone not having the access to the special key for decrypting it.
The majority of securityexperts confesses that end-to-end encryption is undoubtedly the most reliable methods of data privacy. As per this approach, all the conversations, transmitted with end-to-end encrypted messaging applications can only be read by the proposed recipient and not any third person. Such functionality of data encryption is achieved by making use of some unique keys for both encryption and decryption. Only the sender and the receiver can generate these keys.

Two methods of data encryption methods include
- Public Key (Asymmetric) - it makes use of recipient’s public key, accompanied by a private key matching with the public key. After that, one can then send the encrypted message with the public key, which can later on be decrypted by the recipient using the matching private key.
- Private Key (Symmetric) - This is very similar to the Public Key, as both the keys are required to encrypt and decrypt the information. However, with Private Key Encryption, both the keys are ultimately the same, meaning both the parties can encrypt or decrypt the data.
Once the end-to-end encryption is done using a pair of keys, secure communication of data can commence. Data like messages, audio, and video files need to pass the end-to-end encryption method before being sent to the recipient. Until the recipient’s application receive the information, Data will be stored on the server. After the recipient’s notification of the, message the data can be deleted from the server.
These methods of data encryption are very similar as both allow encryption to users protecting it from any third party, who is not authorized to access the information. Both the methods are extremely effective when it comes to protecting messages and other communication from those having no authority to access the data.
When it about security of data over the Internet, a normal won’t be concerned about the topics like end-to-end encryption and more. Indeed, we do not tend to worry about safety of private messages and the end-to-end encryptionwhen chatting with friends or relatives.
But these days, data communication via the Internet comprises online shopping, banking,airline tickets, scanning personal documents, etc. That’s why it has become essential to understand the ideology of end-to-end encrypted messaging application. Supporting such functionality proves to be extremely important, especially for business enterprises as you get to save all the valuable data from eavesdroppers.
Following the trends in the growth of chatting applications, security issues isn’t secret anymore. It is a big point of concern for its users and the developers. With this, Users have now become choosy and are paying more attention to the safety of their private communications.
Developers implementingthe pioneering end-to-end encryption technology have been successful in providing secured data transmission. End-to-end encrypted messaging applicationsenables a desirable level of data privacy. The best about it is that even if oneseeks a method to intercept the messages, he won’t be able to decrypt itwithout having the secret key.
End-to-end encryption was primarily designed for ensuring that any malefactor isn’t able to decipher the data, even if he gets an access to it. Since any server is not involved in generating the key. Only encrypted messages are made visible, when transmitted between the users. So, no third party can have access to the data, even if there is a data leak.
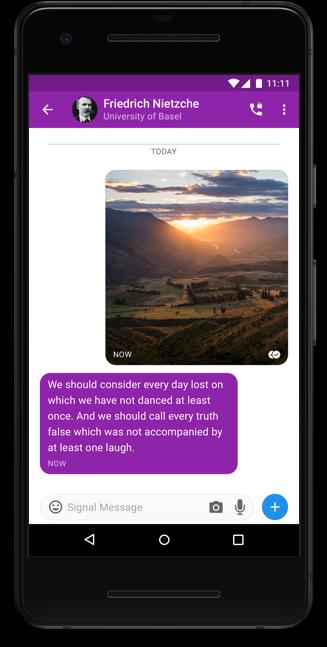
Encrypted messaging Applications like Signal provides an easy way for users to keep their peer-to-peer and group conversations secure simply by offering end-to-end encryption to the users’ messages, keeping out private information safe from those prying eyes. It is a phenomenal method to prevent folks from monitoring and intercepting messages.
Source: https://signal.org/











No Comments